


Continuous Cyber Compliance Automation Technology
Continuous Cyber Compliance Automation Technology
Continuous Cyber Compliance Without Continuous Pain
The Caveonix platform optimizes tedious, incomplete, and expensive cyber compliance programs for more than 50 frameworks, regulations, and mandates.
The Caveonix platform optimizes tedious, incomplete, and expensive cyber compliance programs for more than 50 frameworks, regulations, and mandates.
Book a Demo Today
Book a Demo Today
Book a Demo Today
Trusted by Leaders
Make the Pain Go Away
Sound familiar? With Caveonix these problems are history.

Cumbersome Compliance
Inefficient, expensive, and cumbersome efforts to perform and prove cyber compliance.

Cumbersome Compliance
Inefficient, expensive, and cumbersome efforts to perform and prove cyber compliance.

Cumbersome Compliance
Inefficient, expensive, and cumbersome efforts to perform and prove cyber compliance.

Stretched Security
Expert resources diverted too frequently from security priorities to provide compliance support.

Stretched Security
Expert resources diverted too frequently from security priorities to provide compliance support.

Stretched Security
Expert resources diverted too frequently from security priorities to provide compliance support.

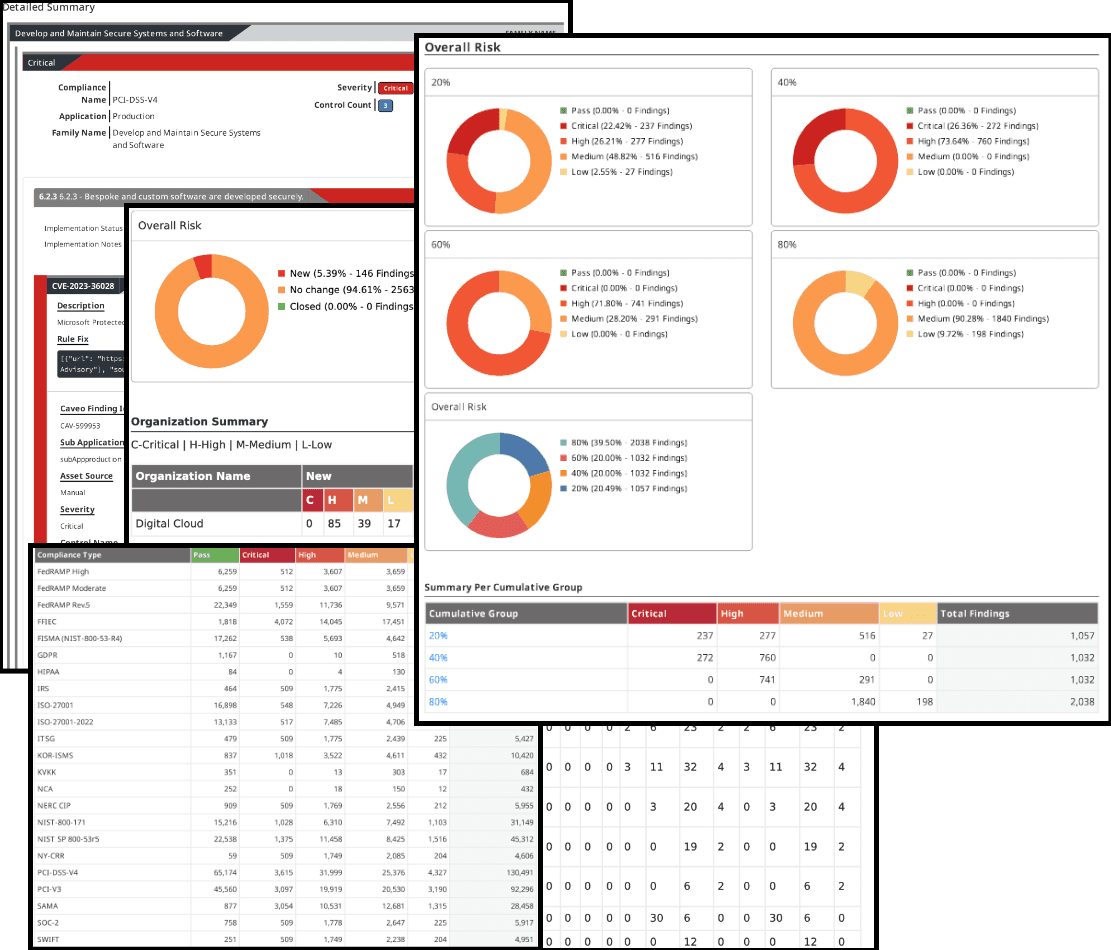
Partial Picture
Outdated, incomplete compliance visibility due to point-in-time information that doesn’t reflect technology and regulatory changes.

Partial Picture
Outdated, incomplete compliance visibility due to point-in-time information that doesn’t reflect technology and regulatory changes.

Partial Picture
Outdated, incomplete compliance visibility due to point-in-time information that doesn’t reflect technology and regulatory changes.

Audit Agony
Late nights pulling together evidence with screenshots and spreadsheets and the stress of not knowing your current compliance posture.

Audit Agony
Late nights pulling together evidence with screenshots and spreadsheets and the stress of not knowing your current compliance posture.

Audit Agony
Late nights pulling together evidence with screenshots and spreadsheets and the stress of not knowing your current compliance posture.
Customer Wins
Our customers get strong hard-dollar ROI results with Caveonix - here are some of their outcomes.

$2M
Reinvest
Savings from legacy software

$2M
Reinvest
Savings from legacy software

$2M
Reinvest
Savings from legacy software

70%
Automate
Reduction in manual workloads

70%
Automate
Reduction in manual workloads

70%
Automate
Reduction in manual workloads

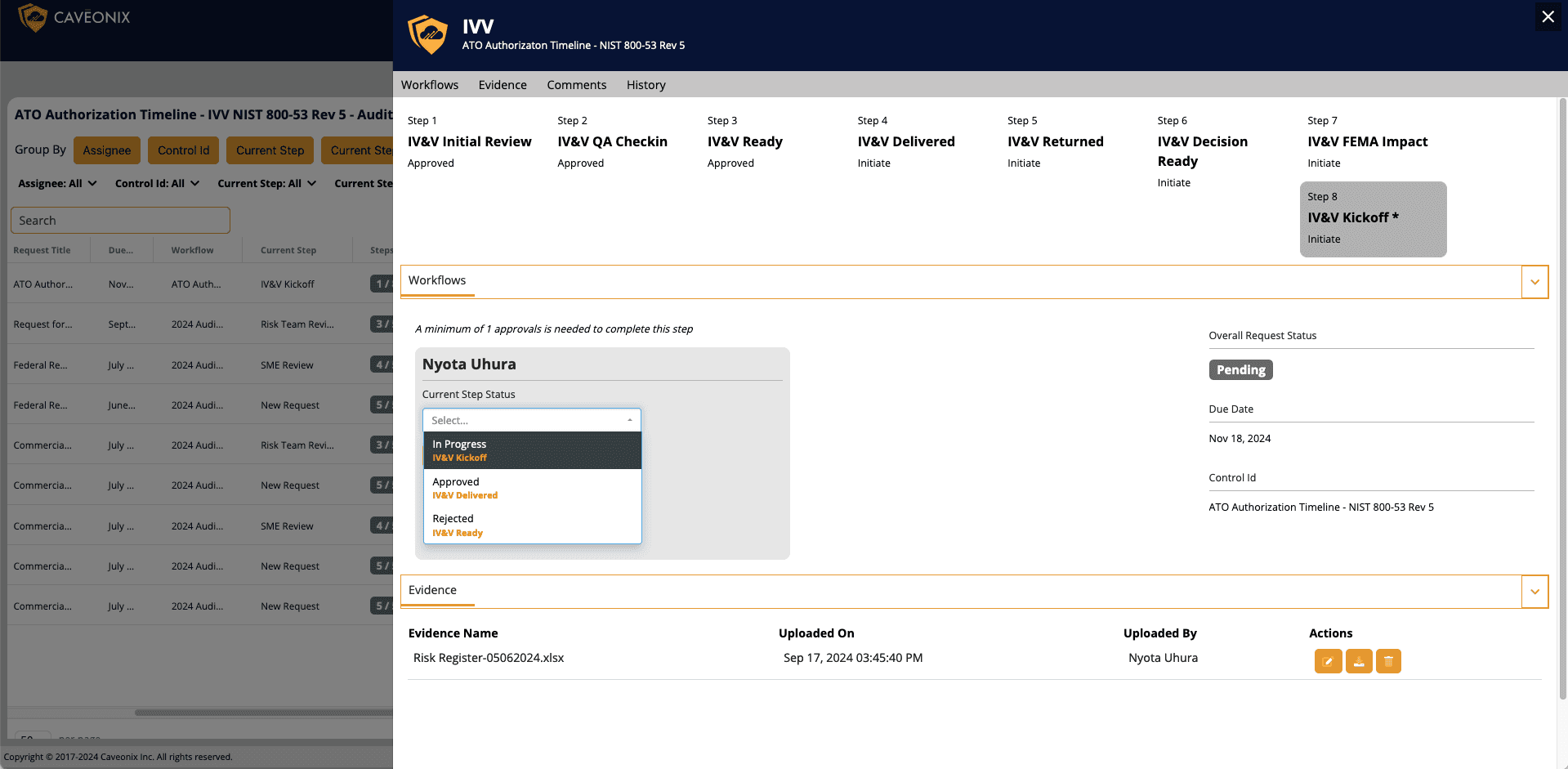
1
Create
ATO build cut from 60 hours to just 1

1
Create
ATO build cut from 60 hours to just 1

1
Create
ATO build cut from 60 hours to just 1
Our Core Capabilities
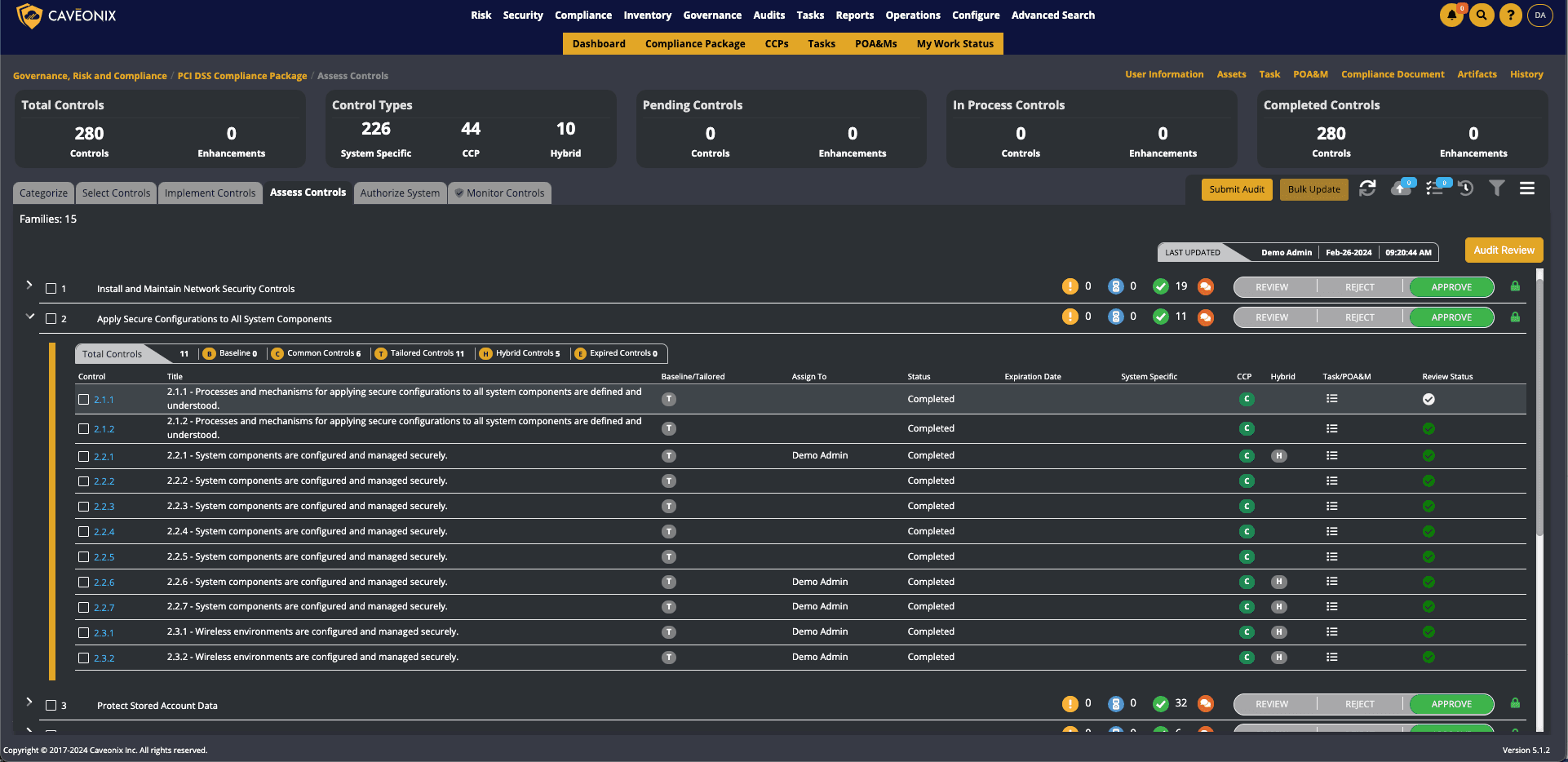
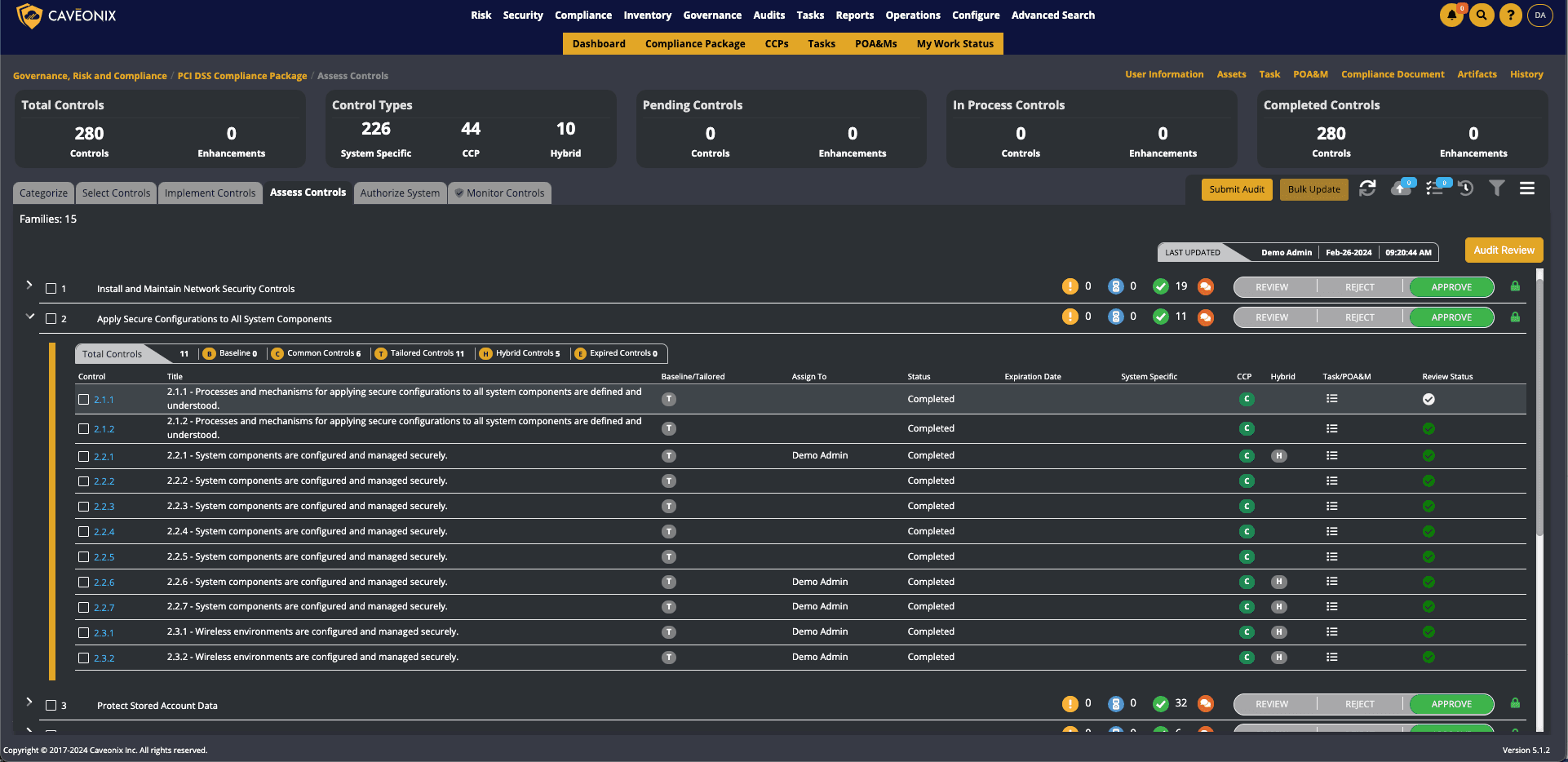
Compliance
Cyber Compliance Confidence
Seamless Integration
Incorporate new mandates, frameworks, and technologies seamlessly in the cloud, on-prem, or hybrid.
Continuous Monitoring
Detect compliance drift as it happens with continuous monitoring.
Automated Documentation
Document compliance posture without asking your security team to create screenshots and spreadsheets.
Learn More
Compliance
Cyber Compliance Confidence
Seamless Integration
Incorporate new mandates, frameworks, and technologies seamlessly in the cloud, on-prem, or hybrid.
Continuous Monitoring
Detect compliance drift as it happens with continuous monitoring.
Automated Documentation
Document compliance posture without asking your security team to create screenshots and spreadsheets.
Learn More
Compliance
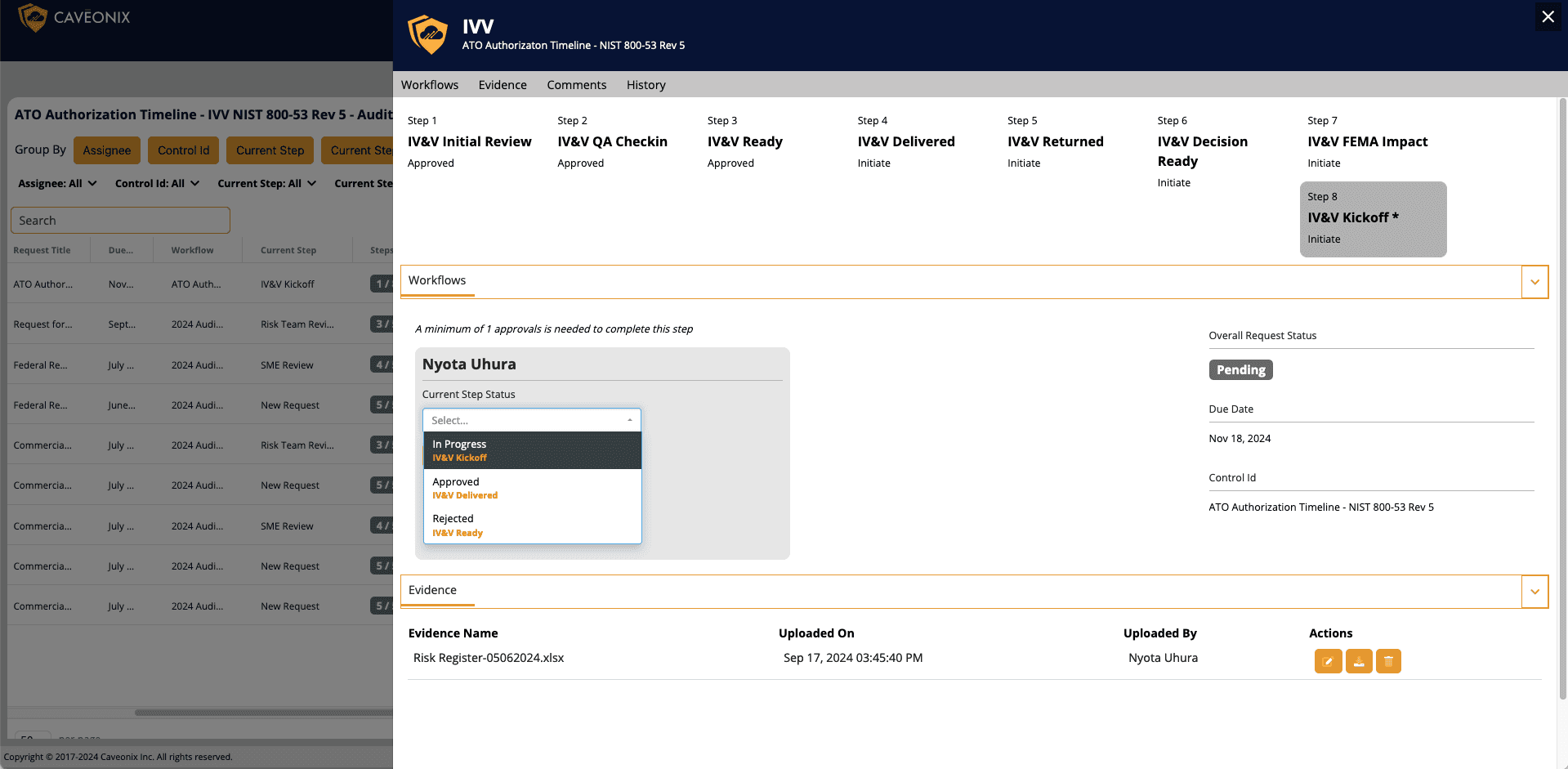
Audit
Risk Management
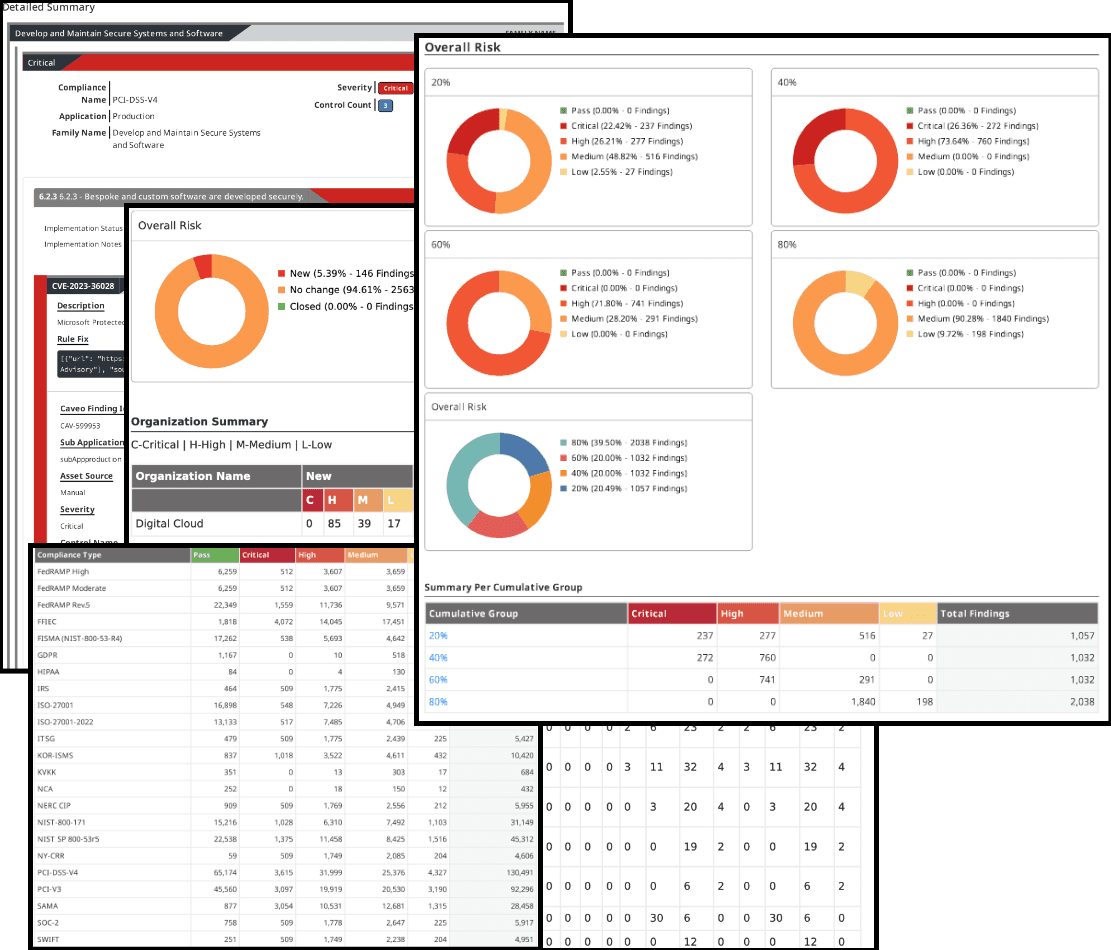
Reporting
Cyber Compliance Confidence
Seamless Integration
Incorporate new mandates, frameworks, and technologies seamlessly in the cloud, on-prem, or hybrid.
Continuous Monitoring
Detect compliance drift as it happens with continuous monitoring.
Automated Documentation
Document compliance posture without asking your security team to create screenshots and spreadsheets.


Compliance
Audit
Risk Management
Reporting
Cyber Compliance Confidence
Seamless Integration
Incorporate new mandates, frameworks, and technologies seamlessly in the cloud, on-prem, or hybrid.
Continuous Monitoring
Detect compliance drift as it happens with continuous monitoring.
Automated Documentation
Document compliance posture without asking your security team to create screenshots and spreadsheets.


Top Resources
Explore More
Explore More
Explore More
Cyber Compliance Doesn’t Have to Be This Hard or Expensive
Contact us to see how Caveonix optimizes compliance for the modern cyber world.
Book a Demo
Cyber Compliance Doesn’t Have to Be This Hard or Expensive
Contact us to see how Caveonix optimizes compliance for the modern cyber world.
Book a Demo
Cyber Compliance Doesn’t Have to Be This Hard or Expensive
Contact us to see how Caveonix optimizes compliance for the modern cyber world.
Book a Demo












